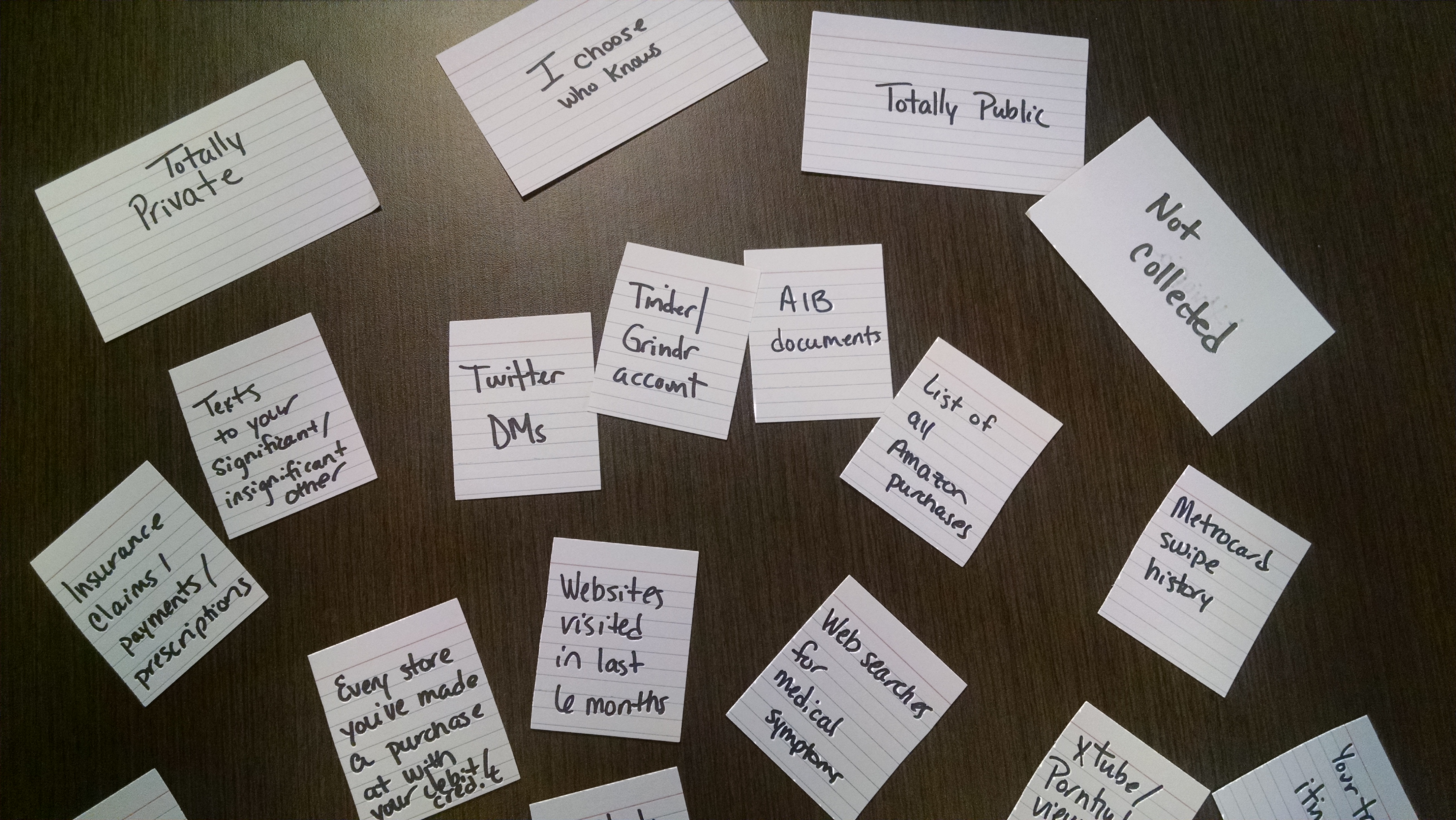
We’ve been working on a framework for a computer science curriculum grounded in global perspectives and multiple identities, with the ultimate goal of fostering ethical innovation. Our first activity to help students think about the intersection of privacy, identity, and data is a card game (available for available for remixing and reuse here). The game, which can be played in one class period, can be adapted to various age groups and classroom activities. We imagine it being used as an introductory activity in a computer science class before a discussion about software development, information architecture, security, big data, or development of algorithms to help students understand how their identity impacts their experience with data collection. No prior technical experience or knowledge is required to play the game, however, and it could easily be used in a course discussion about identity and privilege or global human rights.
The purpose of the original version of the game is to help students:
- Gain awareness of the different types of data collected and stored during online and assumed-to-be offline activities;
- Reflect on what different types of data, and combinations of data, can reveal about our own identity;
- Consider how the perception of harmless data collection changes when viewed through the lens of different identities;
- Talk about the types of data users have no control over and are “essential” to the functioning of the tools; and
- For CS students: discuss the protection of identities and privacy when determining “essential” data for software and services.
At our school, as part of a day-long conversation about race and systemic racism, we were asked to host classes on the intersection of race and privilege. For our course, we deepened our focus of the card game on racial identity, to provide opportunities for students to discuss how their own racial identities impacted their comfort with various types of data collection and use. Modifications are included below.
- We asked students to enter round 2 with the perspective of a) a family member of someone on the no-fly list or b) a friend of someone who was selected for California’s gang database. The two identities highlight the government’s use of race-based watch lists, and how online data is used to profile and select individuals for the lists. There is also an opportunity to discuss how privacy protects not only ourselves, but those we interact with online. We emphasized very explicitly that selection for the lists is not based on any actual crime or doing anything “wrong”, one can be included in the database simply by fitting the profile developed by the database administrators.
- We discussed the connection between privilege and comfort with data collection. If some of us are privileged by systematic data collection (in the form of better recommendations and more efficient tools) while some of us are harmed by data collection (in the form of profiling and exclusion from opportunities or inclusion on watch lists) how do we understand data collection and use to be part of systemic racism?
- How is data collection a form of power? This opens the discussion to our ability to collect data about the government vs their ability to collect data about us. This provided an opportunity to talk about the Third Party Doctrine and how corporations act as a proxy for the government.